What are the three different levels of multilevel security?

Rachel Hickman
Published Feb 19, 2026
What are the three different levels of multilevel security?
The term multi-level arises from the defense community’s security classifications: Confidential, Secret, and Top Secret.
What is MLS model?
Multilevel security or multiple levels of security (MLS) is the application of a computer system to process information with incompatible classifications (i.e., at different security levels), permit access by users with different security clearances and needs-to-know, and prevent users from obtaining access to …
What is multilevel database security?
Multilevel security is a security policy that allows you to classify objects and users based on a system of hierarchical security levels and a system of non-hierarchical security categories. Multilevel security does not rely on special views or database variables to provide row-level security control.
Which is the most commonly used in multi level security access control?
Discretionary access control is the most common: users, at their discretion, can specify to the system who can access their files. Under discretionary access controls, a user (or any of the user’s programs or processes) can choose to share files with other users.
Which of the following is a characteristic of multilevel access control?
Characteristics of a multilevel-secure system include the following: The system controls access to resources. The system does not allow a storage object to be reused until it is purged of residual data.
What is multilevel authentication?
6.1 What Is Multilevel Authentication? OracleAS Single Sign-On enables you to assign different authentication levels to the applications that it protects. You can then map these authentication levels to specific authentication plugins.
What is MLS policy?
Aimed at benefitting consumers and ensuring a level playing field for brokers, the new policy requires MLS-participating brokers to share listings with other brokers in the MLS within one business day of marketing the property to the public. …
What is multilevel database elaborate?
Briefly, a multilevel database provides granular security for data depending on the sensitivity of the data field and clearance of the user for both writing and reading data.
Is used to enforce multilevel security by categorizing?
Mandatory security mechanisms. These are used to enforce multilevel security by classifying the data and users into various security classes (or levels) and then implementing the appropriate security policy of the organization.
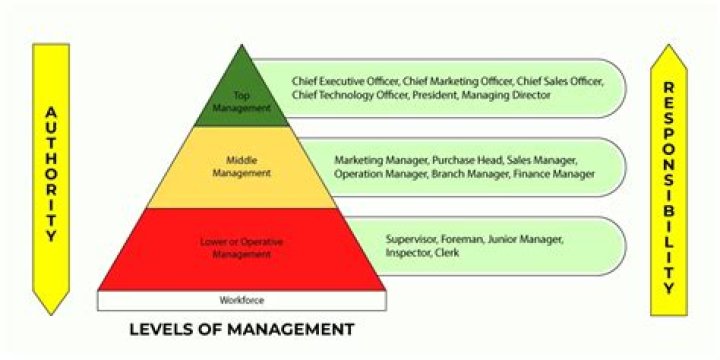
Which Access Control provide multilevel security and is the strictest of all?
Mandatory Access Control (MAC)
Among the different types of access control, Mandatory Access Control (MAC) is considered to be the strictest approach and is based on security level. In this model, the data are classified into different categories and each data has security labels based on classification and users also have classification property.
What are typical security levels multilevel security?
multilevel security is a security policy that allows the classification of data and users based on a system of hierarchical security levels combined with a system of non-hierarchical security categories. A multilevel-secure security policy has two primary goals.
What is multilevel security and why is it important?
There are two contexts for the use of multilevel security. One is to refer to a system that is adequate to protect itself from subversion and has robust mechanisms to separate information domains, that is, trustworthy.
Can a multi layer blockchain security model protect IoT networks?
This paper proposes a Multi layer Blockchain Security model to protect IoT networks while simplifying the implementation. The concept of clustering is utilized in order to facilitate the multi-layer architecture.
What is the best way to develop an enterprise security architecture?
Enterprise Security Architecture—A Top-down Approach 1 SABSA, COBIT and TOGAF and Their Relationships. 2 Using the Frameworks to Develop an Enterprise Security Architecture. 3 A Real-Life Example. 4 Using CMMI to Monitor, Measure and Report the Architecture Development Progress. 5 Conclusion. 6 Endnotes.
What is a multi-layer distributed blockchain network?
The new network model that is based on multi-layer distributed blockchain can be regarded as an organic combination of the blockchain technology and clustering techniques that effectively utilize network clustering performance and capabilities, and significantly improve the overall security and reliability of the IoT.